Ransomware Attacks Surge in 2023, Prompting Global Concern
The State of Ransomware 2023: A Threat Unleashed
Date: May 19, 2023
According to a CyberCube report, the volume of ransomware and extortion attacks is likely to increase in 2023, with additional attempts to compromise IT supply chains and geopolitical targets such as government agencies and non-government organizations. Supply chain attacks, double extortion, and RaaS are some of the ransomware trends that plagued 2022 and will continue to disrupt businesses in 2023.

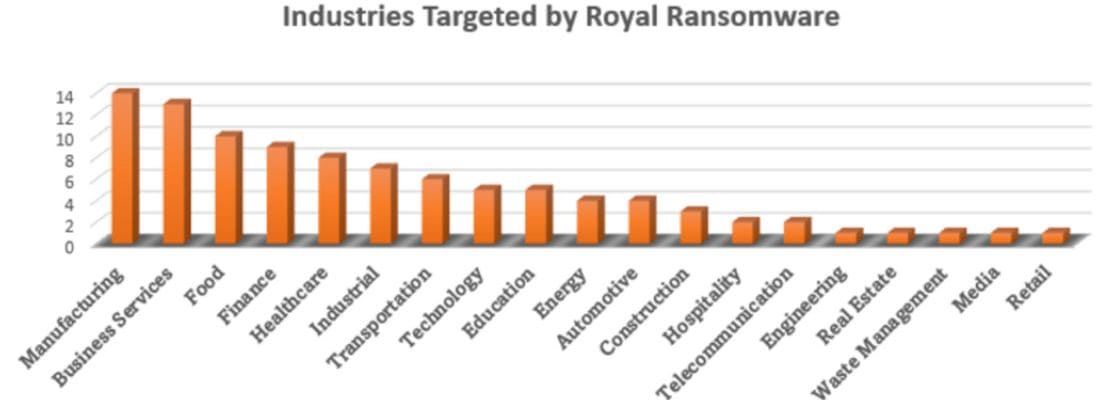
From healthcare to finance, government agencies to small businesses, every corner of the digital landscape has felt the impact of these malicious attacks. The scale and frequency of incidents have reached unprecedented levels, leaving individuals and organizations vulnerable and searching for solutions.
Sophos' annual State of Ransomware, 2023 report shows that 66% of organizations surveyed said they were hit by ransomware in the last year. This is the same attack rate as reported in their 2022 study, suggesting that the rate of ransomware attacks has remained steady despite any perceived reduction in attacks. The education sector reported the highest level of ransomware attacks, with 79% of higher education organizations surveyed and 80% of lower education organizations surveyed saying that they were victims of ransomware.
The most common reported root cause of attack was an exploited vulnerability (involved in 36% of cases), followed by compromised credentials (involved in 29% of cases).
Data encryption from ransomware is at the highest level in four years with adversaries succeeding in encrypting data in 76% of attacks. Furthermore, in 30% of cases where data was encrypted, data was also stolen, suggesting this “double dip” method (data encryption and data exfiltration) is becoming commonplace.
Incident costs rise significantly when ransoms are paid. 46% of organizations surveyed that had their data encrypted paid the ransom and got data back. Larger organizations were far more likely to pay with more than half of businesses with revenue of $500 million or more admitting that they paid the ransom.
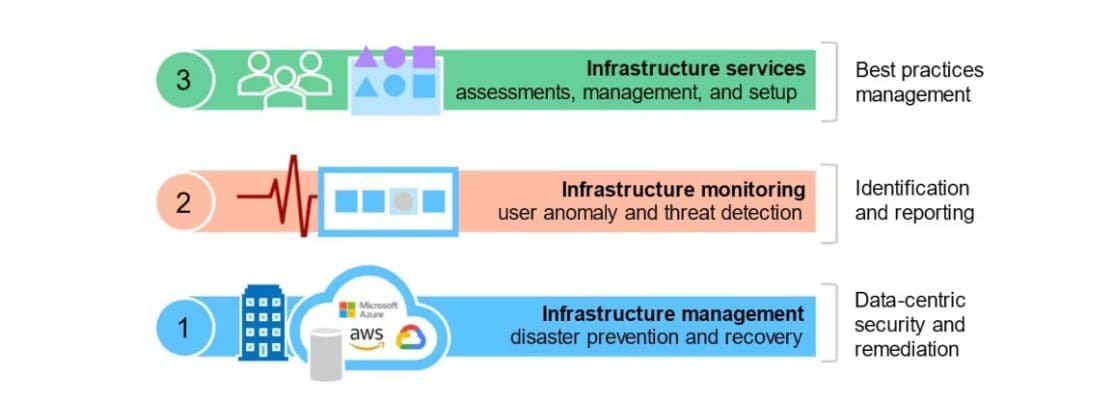
Mitigating the risk of ransomware attacks requires a multi-faceted approach that includes technical, operational, and educational measures. Best practices to help defend against ransomware and other cyberattacks are:
Strengthen defensive shields, including:
- Security tools that defend against the most common attack vectors, including endpoint protection with strong anti-exploit capabilities to prevent exploitation of vulnerabilities, and Zero Trust Network Access (ZTNA) to thwart the abuse of compromised credentials.
- Adaptive technologies that respond automatically to attacks, disrupting adversaries and buying defenders time to respond.
- 24/7 threat detection, investigation and response, whether delivered in-house or by a specialist Managed Detection and Response (MDR) provider.
Optimize attack preparation, including making regular backups, practicing recovering data from backups, and maintaining an up-to-date incident response plan.
Maintain good security hygiene, including timely patching and regularly reviewing security tool configurations.
Apart from the above practices, ensure implementing strong security measures, developing robust backup and disaster recovery plans, and educating employees on safe computing practices, businesses, and organizations to reduce the risk of falling victim to ransomware attacks.

Ransomware should be at the top of your list of concerns when it comes to securing your network, even though it may not be the most recent news. While many businesses may not be able to achieve zero-trust security, there are currently tested methods for reducing your risk of ransomware attacks and containing them once they have been discovered so that they don't spread. New security measures and technologies have also made it possible for businesses to bounce back quickly and avoid the expensive duration of downtime. Although ransomware remains a threat, it doesn't have to be a necessary evil for conducting business.
