Transform your digital defense with MDRaaS
Managed Detection and Response as a Service: Empowering rapid response to evolving threats while facilitating the path to cyber resilience and maturity.
Get Started
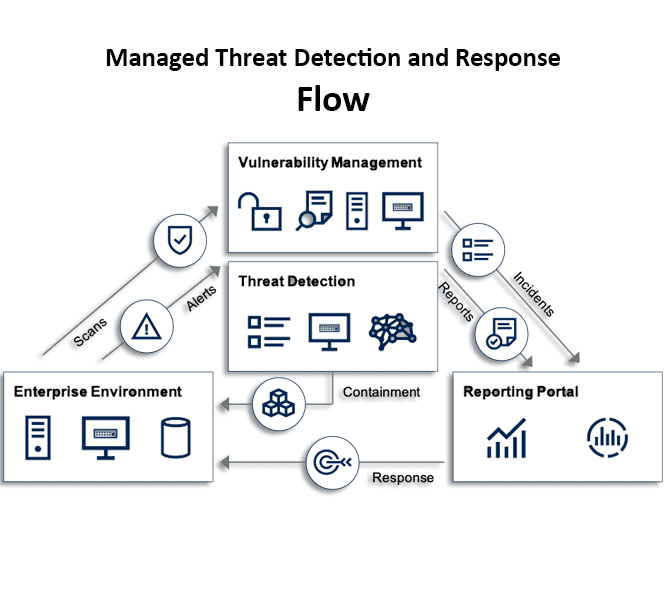
MDR services combine human expertise, threat intelligence, and a variety of network, endpoint, and cloud detection technologies to assist organizations in detecting and responding to threats, strengthening their security posture, and reducing risk exposure.
All organizations require the ability to detect, contain, and respond to threats, but the internal resource burden is significant. MDR services allow businesses to achieve enterprise-level cyber security capabilities at a fraction of the cost of developing the same capabilities in-house.
CloudFence.ai’s MDR offers a comprehensive set of security services, such as alert monitoring, alert prioritization, investigation, and threat hunting. It correlates and prioritizes advanced threats by applying artificial intelligence models to endpoint, network, and server data. CloudFence Technologies threat researchers can work with organizations to provide a detailed remediation plan after investigating prioritized alerts.
Managed Detection and Response for Better Cybersecurity Results
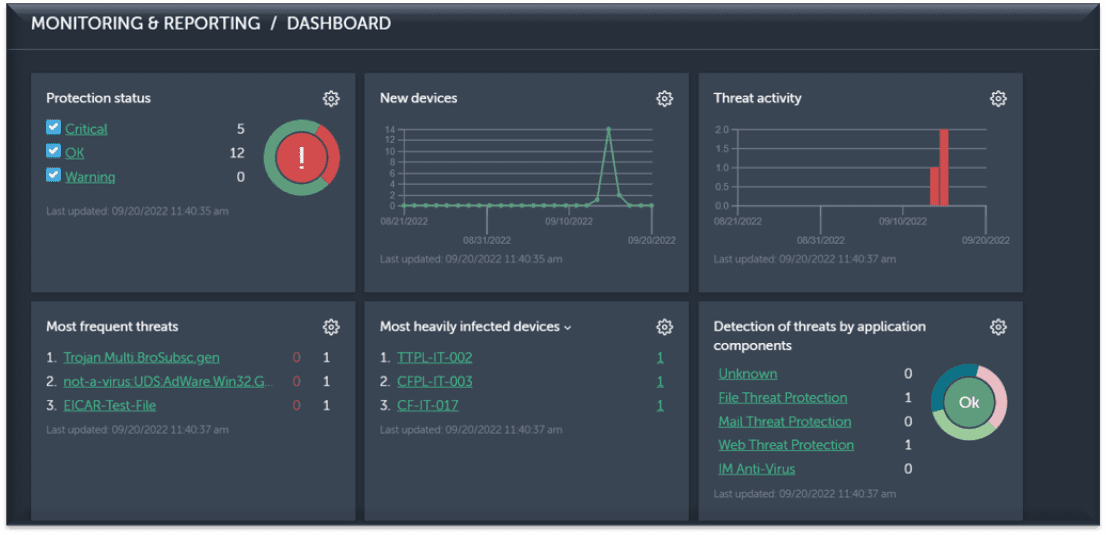
CloudFence Technologies has numerous technology patents, demonstrating our innovative culture. At CloudFence, we strive to create tech that can enhance and strengthen our practise. Our skilled threat hunters, certified security analysts, and CSIRT (Security Incident Response Teams) assist organizations in large-scale threat hunting, automated threat investigation and containment, and aid in incident response orchestration.
CloudFence Technologies MDR is a managed security service that meets you where you are and helps you achieve your security and business goals.
Choose one of the two service options that best meet your needs.
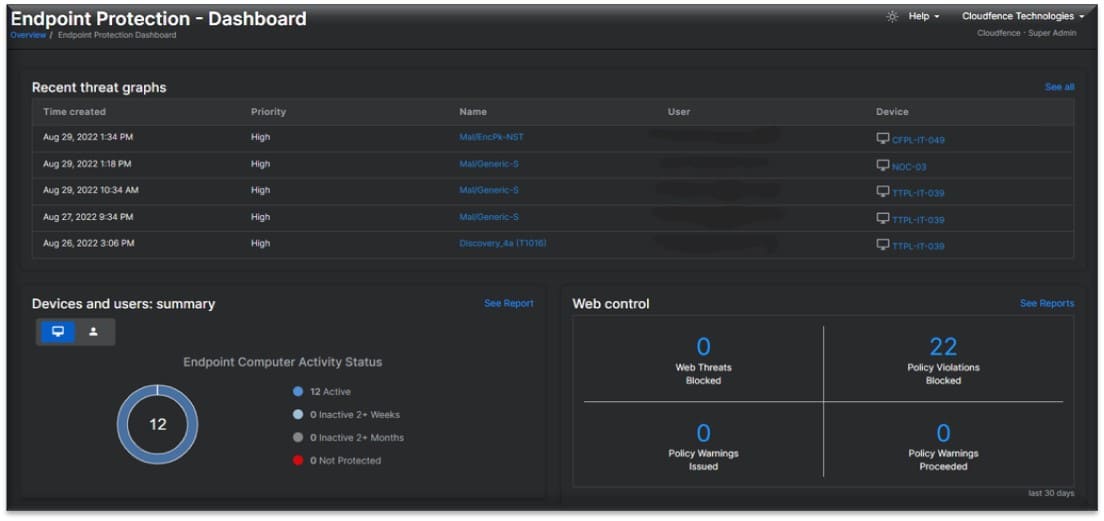
CloudFence Technologies offers cutting-edge endpoint security that includes real-time visibility, analysis, protection, and remediation. We prevent malware infection, detect and deflect potential threats in real-time, and automate response and remediation procedures with customizable playbooks.
CloudFence Technologies automatically and efficiently detect and stops breaches in real time. Key capabilities of endpoint detection and response:
Detect and deflect potential threats in real-time, even on compromised devices.
Based on risk mitigation policies, detect and control rogue devices and applications.

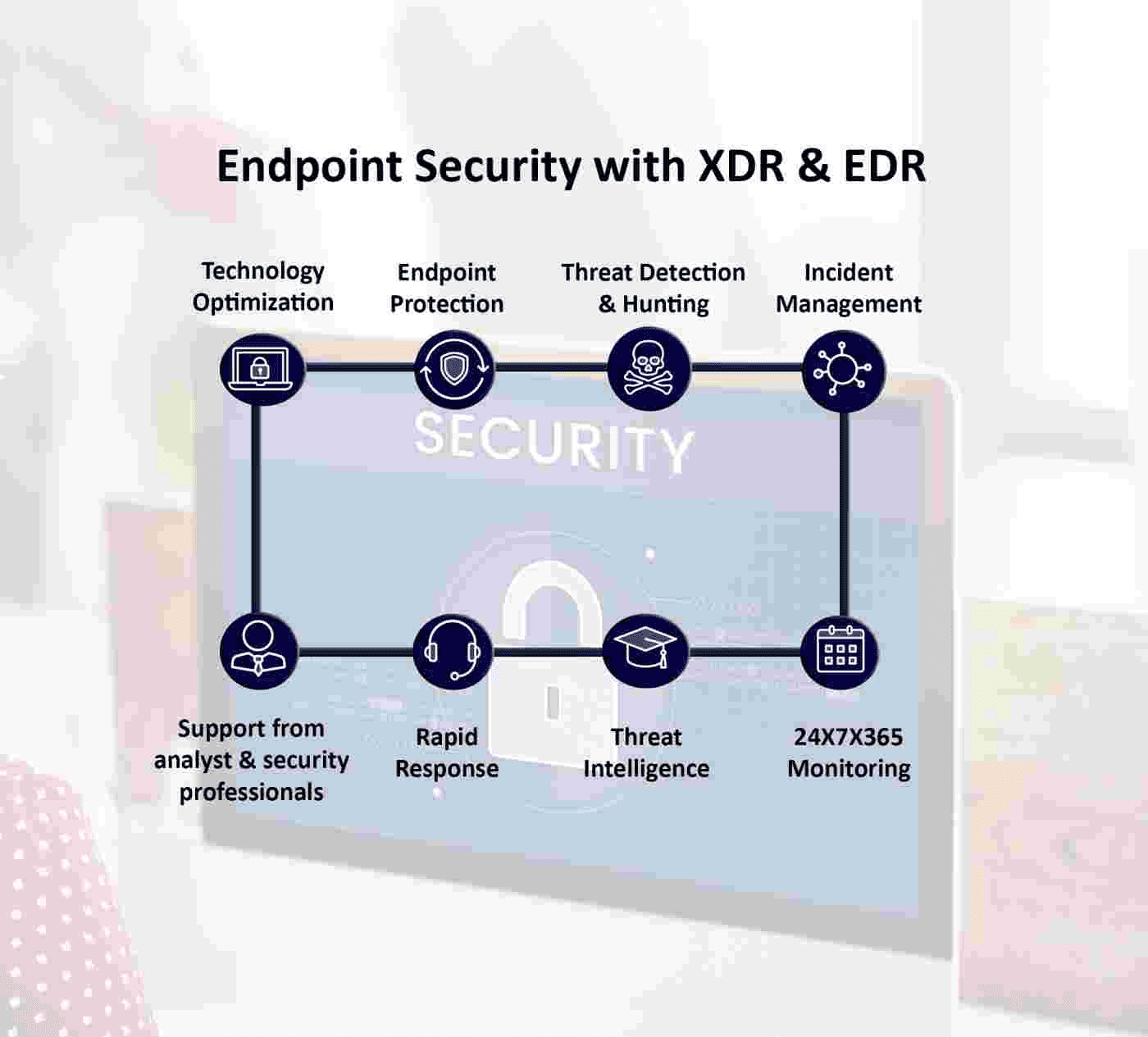
Increase visibility and actionable insights for your security operations team to automate threat response across networks, clouds, endpoints, email, and applications. CloudFence's open and extensible approach to XDR enables customers to leverage our comprehensive portfolio of solutions as well as their existing investment in the company's security infrastructure. With additional telemetry sources and contextual insights, this method assists customers in better detecting, investigating, and prioritizing incidents. The XDR offering from CloudFence Technologies provides out-of-the-box playbooks and rich automation, enabling rapid remediation and mitigation of dangerous threats.
With automation capabilities, you can reduce noise and alleviate skill shortages while increasing the value of your security team's resources.
With a multi-vector, multi-vendor approach optimized for open environments, you can gain visibility and actionable threat intelligence.
Fill security gaps while anticipating and preparing for future threats. Improve your strength every day by working hard.
Give your security teams the tools they need to prioritize threats, conduct streamlined investigations, and make evidence-based recommendations..

Drive Business Value-Managed Detection and Response allow businesses to extract more value from their business model in the following ways:
Copyright © 2021 CloudFence. All Rights Reserved. | Privacy Policy