Cyber Security Operations and Management
SOC Compliance and Managed Security Services for Your Business Assets
Get Started

With the growing threat of cyberattacks, Cyber SOC has become a crucial part of every organization to sustain operations, remain profitable, and achieve and maintain regulatory compliance. However, achieving a high level of security maturity through an in-house SOC can be costly and time-consuming. As a result, many organizations are considering outsourced security services, such as SOC-as-a-Service (SOCaaS) offerings.
CloudFence Technologies' approach to security operations support begins with the identification of customer requirements, followed by implementation, monitoring, tuning, and the use of appropriate tools. We understand the challenges of keeping an organization secure, and we draw on our experience in implementing Security Operations Centers for both small and large organizations.
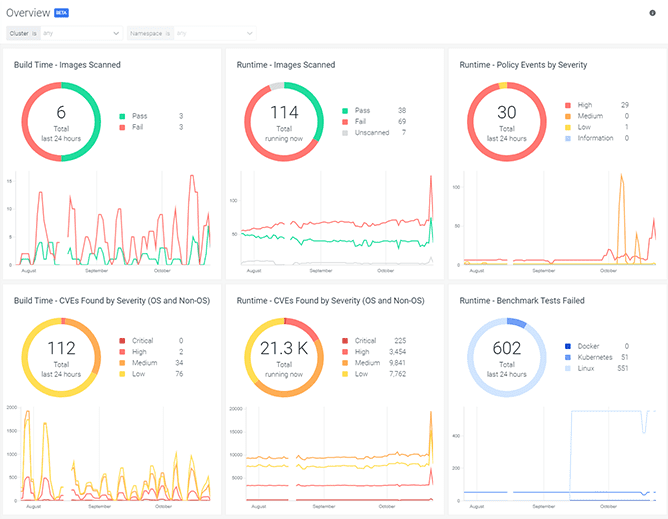
CloudFence Technologies' Security Operation Center Services are based on cutting-edge technologies and a highly qualified team that operates 24x7. The team effectively monitors, analyses, and responds to cybersecurity issues.
Our managed SOC services assist you in strengthening your organization's security posture by identifying and resolving all significant network vulnerabilities. When it comes to managing the customer environment, we are the most sought-after. We have one of India's most desirable, advanced, and sophisticated security operations centers.
A SOC-as-a-Service offering allows a company to delegate security responsibility to a team of security experts. These managed SOC services offer a variety of advantages to an organization, including:
Improved Security Staffing
Reduced Total Cost of Ownership
Up-to-Date Security
Increased Security Maturity
Access to Specialized Security Expertise
Get real-time, round-the-clock incident management that includes cyber threat monitoring, detection, analysis, and response management. Gain complete visibility into all risks and threat scenarios across the entire IT landscape. Integrate advanced analytics and intelligent cybersecurity solutions to predict risks, ensure end-to-end health monitoring, strengthen system security standards, and agile threat remediation
Monitor, evaluate, and manage user roles and activity across all enterprise functionalities. Assign access controls, integrate deep user behavior analytics, monitor end-user activities, manage identities and passwords, and authorize special security administration roles.


When you outsource your SOC requirements to CloudFence Technologies, you get ongoing personalized support and advice from our world-class security operations center. This includes the following aspects:
Copyright © 2021 CloudFence. All Rights Reserved. | Privacy Policy